To know, to have, or to be
What kinds of things need to be secured? What kinds of things can be used to secure what needs to be secured? 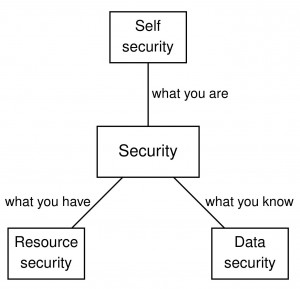
There is a slogan that security is based on three kinds of things:
- what you know: passwords, digital keys…
- what you have: smartcards, physical keys…
- what you are: fingerprints, handwriting…
How do we know that there are no other kinds things? We know because there are just three ways of sharing things:
- What I know I can copy and give it to you, so that we both know it. (We call such things data.)
- What I have I cannot copy, but I can give it to you, so that you have it and I don’t. (We call such things objects or resources.)
- What I am I cannot either copy or give to you, and only I am me. (We call what such things identity or self.)
Please don’t get confused by the fact that smartcards can be cloned and that biometric properties can be faked. The point is here that copying data is essentially costless, whereas copying smartcards or cloning people is not. CDs and DVDs can also be copied, but the music and the film industries were thriving with that problem, and they have badly suffered from the costless data streams.
Basic security properties and goals
At the highest level, security research is subdivided into studying the resource security of what-you-have, and the data security of what-you-know. A crude taxonomy of the security properties studied in these two areas is on the picture below.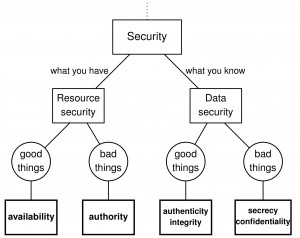
- Within resource security, the requirement that the good resource uses do happen is called availability; the prevention of the bad resource uses is called authorization.
- Within data security, the requirement that the good data flows do happen is called authenticity, or integrity; the prevention of the bad data flows is called secrecy, or confidentiality.
There are, of course, many different ways to use the same words, and many people use the words “confidentiality”, “integrity” etc, in ways not covered by the above taxonomy. But we need some definitions, and these seem useful. See this post for more.
What about the third branch: self security of what-you-are?
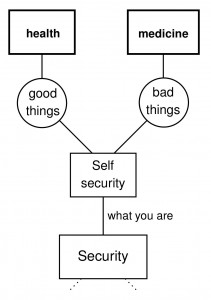 For better or for worse, that’s what they study in medicine and health sciences. Security research still didn’t really connect up with that area, although some biometric researchers of course study what-you-are. There have been various efforts towards biologically inspired security and towards viewing security as immunity. But the real relations between what-you-know and what-you-have and what-you-are are still waiting to be clarified ;)
For better or for worse, that’s what they study in medicine and health sciences. Security research still didn’t really connect up with that area, although some biometric researchers of course study what-you-are. There have been various efforts towards biologically inspired security and towards viewing security as immunity. But the real relations between what-you-know and what-you-have and what-you-are are still waiting to be clarified ;)

The distinction between resources and data in the discussion and in the definitions of data security and resource security emphasizes how data can be treated differently from resources in that data can be copied. With appropriate access control in place, the copying of data can be limited. In such situation data can also be seen as a resource. When we discuss resource security in more detail we will emphasize what data and resources can have in common, allow data to be considered as a resource and discuss resource security in its most general sense. Data security focuses on the security aspects of data that are needed when data can be copied and cannot be considered a resource. This makes the access control mechanisms that are needed to prevent the copying of data a special subject of data security.
My main goal with this taxonomy was to try to explain the division of security methods into resource security (access controls, security models…) and data security (information flows, cryptography…). It is often puzzling how little do these two families of methods have in common. Why are they so different? I proposed one possible answer: Because one protects what you have, and the other one what you know.
I think this is not a bad answer to start with, but it is good to admit: it is definitely not a complete answer. It is an oversimplification. In one way or another, almost every answer is an oversimplification. While it is useful to think of resource security as “protecting what you have” and data security as “protecting what you know”, there is definitely more to it – as I hope we shall see later.
In this oversimplification, we hide under the carpet the fact that data are a special kind of a resource. In spite of that fact, data security methods are quite different from resource security methods, just like the methods of biology are quite different from the methods of physics, although life is a special kind of a physical process. In that sense, it is a justified oversimplification.
But you are pointing to another aspect of the same fact: When data are secured, they are not freely copiable any more, and they become a subject of resource security!
Thanks for this!
Some recent literature has suggested that there is a fourth branch: Where you are.
The literature I’ve read (and I’m happy to generate citations if you’d like) claim that mobile devices contain GPS and other location-aware technologies that help establish a persons locations. This technology could be used to help support an authorization request.
I think the claim merits consideration. Not so much for the mobile device/GPS technology angle (which can be spoofed) — but for the idea that if cyber is borderless, costless communication — then the development of this branch could bring a semblance of traditional, real-world security into cyber.